unexpected-changesets
The unexpected-changesets command produces a list of changesets that were run in the database but do not exist in the current changelog.
Uses
The unexpected-changesets command is typically used to detect and compare the changes between the DATABASECHANGELOG table and the current changelog. If any of the changesets in the DATABASECHANGELOG table do not exist in the current changelog, the unexpected-changesets command will detect those changesets and produce them in your output.
The unexpected-changesets command also produces all the changesets that were previously deployed and deleted from your current changelog.
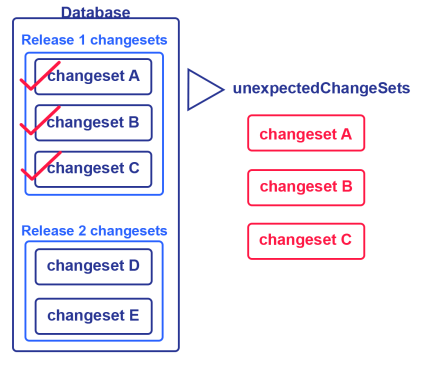
The following image shows the changelog file, which includes changesets for release 1 that are already applied to the database but removed from the changelog file and new changesets for release 2 that are not applied to the database. Running the unexpected-changesets command will produce the number of changesets applied for release 1.
So, if you want to identifying unexpected changesets that were previously applied to the database, run the unexpected-changesets command.
Syntax
To run the unexpected-changesets command, specify the driver, classpath, and URL in the Liquibase properties file. For more information, see Create and Configure a liquibase.properties File. You can also specify these properties in your command line.
Then run the unexpected-changesets command:
liquibase unexpected-changesets --changelog-file=example-changelog.xmlBy default, the output shows the number of unexpected changesets. To see the list of unexpected changesets, add the --verbose flag:
liquibase unexpected-changesets --verbose --changelog-file=example-changelog.xmlCommand parameters
| Attribute | Definition | Requirement |
|---|---|---|
|
|
The root changelog |
Required |
|
|
The JDBC database connection URL. See Using JDBC URL in Liquibase. |
Required |
|
|
Specifies the changeset contexts to match. Contexts are tags you can add to changesets to control which changesets are executed in any particular migration run. Note: If you use Liquibase 4.23.0 or earlier, use the syntax |
Optional |
|
|
Name of the default catalog to use for the database connection |
Optional |
|
|
Name of the default schema to use for the database connection. If Note: In the properties file and Note: In Liquibase 4.12.0 and later, you can use mixed-case schema names if you set |
Optional |
|
|
The JDBC driver class |
Optional |
|
|
The JDBC driver properties file |
Optional |
|
|
Specifies the changeset labels to match. Labels are tags you can add to changesets to control which changesets will be executed in any migration run. |
Optional |
|
|
Password to connect to the target database. Tip: It is a best practice to store sensitive data in a Secrets Management tool with Liquibase Pro. |
Optional |
|
|
Username to connect to the target database. Tip: It is a best practice to store sensitive data in a Secrets Management tool with Liquibase Pro. |
Optional |
|
|
Specifies the detail level of the command's output. Default: |
Optional |
| Attribute | Definition | Requirement |
|---|---|---|
|
|
The root changelog |
Required |
|
|
The JDBC database connection URL. See Using JDBC URL in Liquibase. |
Required |
|
|
Specifies the changeset contexts to match. Contexts are tags you can add to changesets to control which changesets are executed in any particular migration run. Note: If you use Liquibase 4.23.0 or earlier, use the syntax |
Optional |
|
|
Name of the default catalog to use for the database connection |
Optional |
|
|
Name of the default schema to use for the database connection. If Note: In the properties file and Note: In Liquibase 4.12.0 and later, you can use mixed-case schema names if you set |
Optional |
|
|
The JDBC driver class |
Optional |
|
|
The JDBC driver properties file |
Optional |
|
|
Specifies the changeset labels to match. Labels are tags you can add to changesets to control which changesets will be executed in any migration run. |
Optional |
|
|
Password to connect to the target database. Tip: It is a best practice to store sensitive data in a Secrets Management tool with Liquibase Pro. |
Optional |
|
|
Username to connect to the target database. Tip: It is a best practice to store sensitive data in a Secrets Management tool with Liquibase Pro. |
Optional |
|
|
Specifies the detail level of the command's output. Default: |
Optional |
| Attribute | Definition | Requirement |
|---|---|---|
|
|
The root changelog |
Required |
|
|
The JDBC database connection URL. See Using JDBC URL in Liquibase. |
Required |
|
|
Specifies the changeset contexts to match. Contexts are tags you can add to changesets to control which changesets are executed in any particular migration run. Note: If you use Liquibase 4.23.0 or earlier, use the syntax |
Optional |
|
|
Name of the default catalog to use for the database connection |
Optional |
|
|
Name of the default schema to use for the database connection. If Note: In the properties file and Note: In Liquibase 4.12.0 and later, you can use mixed-case schema names if you set |
Optional |
|
|
The JDBC driver class |
Optional |
|
|
The JDBC driver properties file |
Optional |
|
|
Specifies the changeset labels to match. Labels are tags you can add to changesets to control which changesets will be executed in any migration run. |
Optional |
|
|
Password to connect to the target database. Tip: It is a best practice to store sensitive data in a Secrets Management tool with Liquibase Pro. |
Optional |
|
|
Username to connect to the target database. Tip: It is a best practice to store sensitive data in a Secrets Management tool with Liquibase Pro. |
Optional |
|
|
Specifies the detail level of the command's output. Default: |
Optional |
| Attribute | Definition | Requirement |
|---|---|---|
|
|
The root changelog |
Required |
|
|
The JDBC database connection URL. See Using JDBC URL in Liquibase. |
Required |
|
|
Specifies the changeset contexts to match. Contexts are tags you can add to changesets to control which changesets are executed in any particular migration run. Note: If you use Liquibase 4.23.0 or earlier, use the syntax |
Optional |
|
|
Name of the default catalog to use for the database connection |
Optional |
|
|
Name of the default schema to use for the database connection. If Note: In the properties file and Note: In Liquibase 4.12.0 and later, you can use mixed-case schema names if you set |
Optional |
|
|
The JDBC driver class |
Optional |
|
|
The JDBC driver properties file |
Optional |
|
|
Specifies the changeset labels to match. Labels are tags you can add to changesets to control which changesets will be executed in any migration run. |
Optional |
|
|
Password to connect to the target database. Tip: It is a best practice to store sensitive data in a Secrets Management tool with Liquibase Pro. |
Optional |
|
|
Username to connect to the target database. Tip: It is a best practice to store sensitive data in a Secrets Management tool with Liquibase Pro. |
Optional |
|
|
Specifies the detail level of the command's output. Default: |
Optional |
| Attribute | Definition | Requirement |
|---|---|---|
|
|
The root changelog |
Required |
|
|
The JDBC database connection URL. See Using JDBC URL in Liquibase. |
Required |
|
|
Specifies the changeset contexts to match. Contexts are tags you can add to changesets to control which changesets are executed in any particular migration run. Note: If you use Liquibase 4.23.0 or earlier, use the syntax |
Optional |
|
|
Name of the default catalog to use for the database connection |
Optional |
|
|
Name of the default schema to use for the database connection. If Note: In the properties file and Note: In Liquibase 4.12.0 and later, you can use mixed-case schema names if you set |
Optional |
|
|
The JDBC driver class |
Optional |
|
|
The JDBC driver properties file |
Optional |
|
|
Specifies the changeset labels to match. Labels are tags you can add to changesets to control which changesets will be executed in any migration run. |
Optional |
|
|
Password to connect to the target database. Tip: It is a best practice to store sensitive data in a Secrets Management tool with Liquibase Pro. |
Optional |
|
|
Username to connect to the target database. Tip: It is a best practice to store sensitive data in a Secrets Management tool with Liquibase Pro. |
Optional |
|
|
Specifies the detail level of the command's output. Default: |
Optional |
Note: The username and password attributes are not required for connections and systems which use alternate means of authentication. Also, you can specify database credentials as part of the url attribute.
Default output:
Liquibase Version: 4.9.1
Liquibase Community 4.9.1 by Liquibase
1 unexpected changes were found in DBUSER@jdbc:h2:tcp://localhost:9090/mem:dev
Liquibase command 'unexpected-changesets' was executed successfully.When running unexpected-changesets --verbose:
Liquibase Version: 4.9.1
Liquibase Community 4.9.1 by Liquibase
1 unexpected changes were found in DBUSER@jdbc:h2:tcp://localhost:9090/mem:dev
liquibase-internal::1652108822075::liquibase
Liquibase command 'unexpected-changesets' was executed successfully.